工程名称
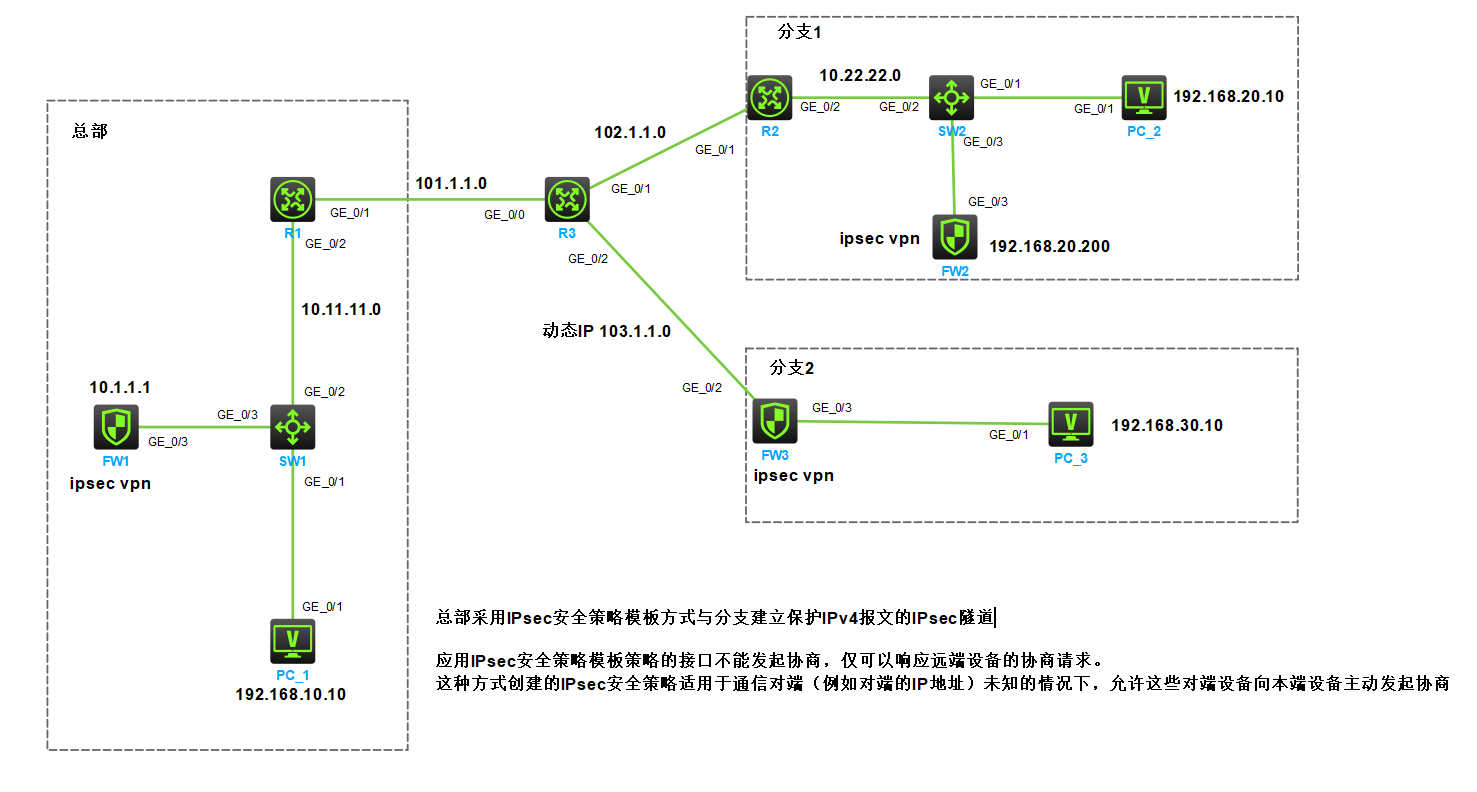
配置和验证华三设备上的总部采用 IPsec 安全策略模板方式与分支建 立保护 IPv4 报文的 IPsec 隧道
网络规划设计
总部的IPsec设备FW1采用旁挂方式,单独的网段接入核心交换机SW1;分支1的IPsec设备FW2采用旁挂方式接入核心交换机SW2,且与PC_2同一网段;分支2的IPsec设备FW3为出口设备,且出口公网IP地址为动态获取。
总部与分支1(静态公网IP地址)的IKE第一阶段使用主模式;总部与分支2(动态公网IP地址)的IKE第一阶段使用主动模式(野蛮模式)
需求:
总部和分支均能访问R3的环回接口地址3.3.3.3
分支FW2、FW3和总部FW1之间建立IPsec隧道,对分支网络与总部网络之间的数据进行安全保护
配置思路
- 先完成IP地址配置,PC能与3.3.3.3 互通 (需要做PAT)
- 总部出口路由器配置NAT SERVER 映射旁挂防火墙FW1
- 分支1的 R2 路由器配置静态公网IP地址
- 分支2的 FW2 防火墙配置动态公网IP地址
- 总部的SW1为核心交换机,PC1的网关在SW1上
- 分支1的SW2为核心交换机,PC2的网关在SW2上
- 分支2的的网关在FW3上
- 当分支机构为静态公网IP地址时ike协商使用main模式
- 当分支机构为动态公网IP地址时ike协商使用aggressive模式
- 使用IKE协商方式建立IPsec SA,采用ESP安全协议
- IKE协商采用预共享密钥认证方式
- 总部FW1采用IKE安全策略模板方式,分支FW2和FW3采用IKE安全策略方式
- 由于只验证ipsec vpn理论,三台防火墙的策略配置了any安全策略
实验步骤:
IP地址和路由
- 设备配置IP地址、静态路由、NAT
- 配置完成后各PC能ping通R3上的3.3.3.3;出口设备能ping通对端出口设备的公网IP地址
SW1和SW2上的引流
1、SW1上,配置静态路由,将总部去往分支机构的网段下一跳指向FW1
# 默认路由器用于访问互联网
ip route-static 0.0.0.0 0 10.11.11.1
# 引流的静态路由
ip route-static 192.168.20.0 24 10.1.1.1
ip route-static 192.168.30.0 24 10.1.1.1
2、SW2上,配置策略路由,将分支1去往总部的网段下一跳地址指向FW2
# 配置acl批量分支1去往总部的流量
acl advanced 3666
rule 0 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
# 配置策略路由匹配acl 3666,指定下一跳地址
policy-based-route TO-ZONGBU permit node 10
if-match acl 3666
apply next-hop 192.168.20.200
# 分支1网关上应用策略路由
interface Vlan-interface10
ip policy-based-route TO-ZONGBU
#
R1和R2上配置端口映射
1、R1上配置端口映射,将端口映射到FW1的接口地址10.1.1.1
# udp 500 和 udp 4500
interface GigabitEthernet0/1
nat server protocol udp global current-interface 500 inside 10.1.1.1 500
nat server protocol udp global current-interface 4500 inside 10.1.1.1 4500
#
2、R2上配置端口映射,将端口映射到FW2的接口地址192.168.20.200
# udp 500 和 udp 4500
interface GigabitEthernet0/1
nat server protocol udp global current-interface 500 inside 192.168.20.200 500
nat server protocol udp global current-interface 4500 inside 192.168.20.200 4500
#
FW1配置
将流量区分为两类给后面的ipsec policy调用
- acl 3010 用于分支机构外网出口是静态公网IP地址的ike 主模式
- acl 3020 用于分支机构外网出口是动态公网IP地址或主模式协商有问题 的ike 野蛮模式
- 如果后续需要新增分支机构加入ipsec vpn,可在以上两个acl后直接添加规则
# 总部去往分支1的数据
acl advanced 3010
rule 0 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.20.0 0.0.0.255
# 总部去往分支2的数据
acl advanced 3020
rule 0 permit ip source 192.168.10.0 0.0.0.255 destination 192.168.30.0 0.0.0.255
#
# 配置IPsec安全提议,协商封装报文使用的各种安全协议
ipsec transform-set tran1
# 默认tunnel模式 encapsulation-mode tunnel
# 默认esp封装 protocol esp
esp encryption-algorithm des-cbc
esp authentication-algorithm sha1
# 配置IKE keychain,约定通信双方使用的密钥信息
ike keychain key1
# 对于使用静态公网IP地址的,省个事,直接4个0,这样后面要新增分支不需要修改配置
pre-shared-key address 0.0.0.0 0.0.0.0 key simple 123
# 对于使用动态IP的fqdn,或野蛮模式的
pre-shared-key hostname fenzhi-2 key simple 456
# 配置IKE profile,约定建立IKE SA所需的安全参数
# 使用mian模式的连接
ike profile profile1
keychain key1
local-identity fqdn zongbu
# 后续新增分支可添加match配置
match remote identity fqdn fenzhi-1
# 使用aggressive模式的连接
ike profile profile2
keychain key1
exchange-mode aggressive
local-identity fqdn zongbu
# 后续新增分支可添加match配置
match remote identity fqdn fenzhi-2
# 配置IPsec安全策略模板,用于创建IPsec安全策略
# 用于主模式的模板
ipsec policy-template temp1 10
transform-set tran1
security acl 3010
ike-profile profile1
# 用于野蛮模式的模板
ipsec policy-template temp1 20
transform-set tran1
security acl 3020
ike-profile profile2
# 引用安全策略模板temp1创建一条IKE协商方式的安全策略policy1
# 建立IPsec隧道,保护需要防护的数据流
ipsec policy map1 10 isakmp template temp1
# 配置IKE提议,定义双方进行IKE协商所需的安全参数
# 创建并配置IKE提议1,指定使用预共享密钥认证方式、加密算法、认证算法。
ike proposal 1
encryption-algorithm 3des-cbc
# 默认认证算法 authentication-algorithm sha
# 默认预共享密钥认证 authentication-method pre-share
#
# 在接口下引用IPsec安全策略,对接口上的流量进行保护
interface gigabitethernet 1/0/3
ipsec apply policy map1
FW2配置
# 分支1去往总部的流量
acl advanced 3000
rule 0 permit ip source 192.168.20.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
#
# 配置IPsec安全提议,协商封装报文使用的各种安全协议
ipsec transform-set tran1
# 默认tunnel模式 encapsulation-mode tunnel
# 默认esp封装 protocol esp
esp encryption-algorithm des-cbc
esp authentication-algorithm sha1
# 配置IKE keychain,约定通信双方使用的密钥信息
ike keychain key1
pre-shared-key address 101.1.1.1 255.255.255.255 key simple 123
# 配置IKE profile,约定建立IKE SA所需的安全参数
ike profile profile1
keychain key1
local-identity fqdn fenzhi-1
match remote identity address 101.1.1.1 255.255.255.0
# 配置ISAKMP方式的安全策略,建立IPsec隧道,保护需要防护的数据流
# 创建并配置名为map1的IPsec安全策略,引用安全提议tran1,引用ACL 3000,并指定IPsec隧道的对端地址为101.1.1.1
ipsec policy map1 10 isakmp
transform-set tran1
security acl 3000
remote-address 101.1.1.1
ike-profile profile1
# 配置IKE提议,定义双方进行IKE协商所需的安全参数
# 创建并配置IKE提议1,指定使用预共享密钥认证方式、加密算法、认证算法。
ike proposal 1
encryption-algorithm 3des-cbc
# 默认认证算法 authentication-algorithm sha
# 默认预共享密钥认证 authentication-method pre-share
#
# 在接口下引用IPsec安全策略,对接口上的流量进行保护
interface gigabitethernet 1/0/3
ipsec apply policy map1
FW3配置
# 分支2去往总部的流量
acl advanced 3000
rule 0 permit ip source 192.168.30.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
# NAT调用的acl,排除去往总部的流量进行NAT
acl advanced 3010
rule 0 deny ip source 192.168.30.0 0.0.0.255 destination 192.168.10.0 0.0.0.255
rule 5 permit ip
#
#
ipsec transform-set tran1
esp encryption-algorithm des-cbc
esp authentication-algorithm sha1
#
ipsec policy map1 10 isakmp
transform-set tran1
security acl 3000
remote-address 101.1.1.1
ike-profile profile1
#
ike profile profile1
keychain key1
# 野蛮模式
exchange-mode aggressive
local-identity fqdn fenzhi-2
match remote identity address 101.1.1.1 255.255.255.0
#
ike proposal 1
encryption-algorithm 3des-cbc
#
ike keychain key1
pre-shared-key address 101.1.1.1 255.255.255.255 key simple 456
#
# 在接口下引用IPsec安全策略,对接口上的流量进行保护
# NAT outbound引用acl 3010
interface GigabitEthernet1/0/2
ip address dhcp-alloc
nat outbound 3010
ipsec apply policy map1
#
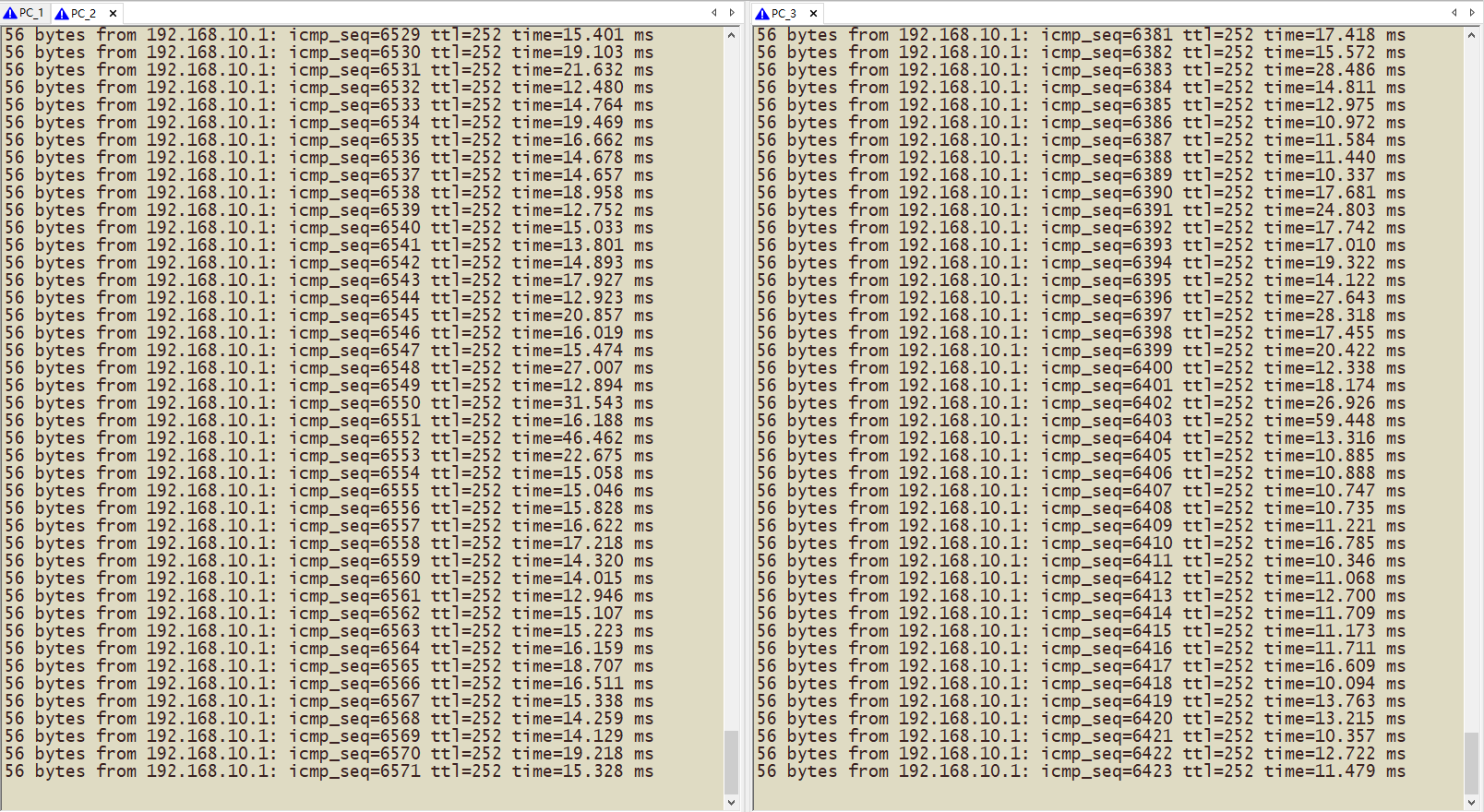
测试结果:
连通性测试
注意:应用了该类IPsec安全策略(FW1上的IPsec安全策略模板方式)的接口不能发起协商,仅可以响应远端设备的协商请求。由于IPsec安全策略模板中未定义的可选参数由发起方来决定,而响应方会接受发起方的建议,因此这种方式创建的IPsec安全策略适用于通信对端(例如对端的IP地址)未知的情况下,允许这些对端设备向本端设备主动发起协商
FW1上查看ike sa
# FW1
<FW1>dis ike sa
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
ID Profile Remote Flag Remote-Type Remote-ID
--------------------------------------------------------------------------------
34 profile2 103.1.1.1 RD FQDN fenzhi-2
38 profile1 102.1.1.2 RD FQDN fenzhi-1
<FW1>
在FW1上观察到,每个ike sa的引用的profile、远端地址、远端类型、远端ID
关于使用序号的问题:文档中说越小越优先,不知是以哪一个匹配项进行的profile选择,待研究
FW1上查看ike sa 详细信息
<FW1>dis ike sa ver
-----------------------------------------------
Connection ID: 34
Outside VPN:
Inside VPN:
Profile: profile2
Transmitting entity: Responder
Initiator cookie: b3ef914a89aa888a
Responder cookie: 168da67159b7262f
Output interface name:
-----------------------------------------------
Local IP/port: 10.1.1.1/4500
Local ID type: FQDN
Local ID: zongbu
Remote IP/port: 103.1.1.1/4500
Remote ID type: FQDN
Remote ID: fenzhi-2
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: 3DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 84747
Exchange-mode: Aggressive
Diffie-Hellman group: Group 1
NAT traversal: Detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index:0xffffffff
Vendor ID sequence number:0x0
-----------------------------------------------
Connection ID: 38
Outside VPN:
Inside VPN:
Profile: profile1
Transmitting entity: Responder
Initiator cookie: 4a8ad70544712029
Responder cookie: cee73f6122f5b8b8
Output interface name:
-----------------------------------------------
Local IP/port: 10.1.1.1/4500
Local ID type: FQDN
Local ID: zongbu
Remote IP/port: 102.1.1.2/1025
Remote ID type: FQDN
Remote ID: fenzhi-1
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: 3DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 84800
Exchange-mode: Main
Diffie-Hellman group: Group 1
NAT traversal: Detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index:0xffffffff
Vendor ID sequence number:0x0
<FW1>
在FW1上观察到,sa 协商使用的各种算法、详细的各种信息,Exchange-mode
FW1上查看ipsec sa 信息
<FW1>dis ipsec sa brief
-----------------------------------------------------------------------------
Tunnel-ID Name Dst Address(port) Protocol SPI
-----------------------------------------------------------------------------
0 template-temp1~ -- ESP --
0 template-temp1~ -- ESP --
1 template-temp1~ <102.1.1.2(1025) ESP 2205382650
1 template-temp1~ >102.1.1.2(1025) ESP 17477209
2 template-temp1~ <103.1.1.1(4500) ESP 558262863
2 template-temp1~ >103.1.1.1(4500) ESP 1974871094
3 template-temp1~ -- ESP --
3 template-temp1~ -- ESP --
<FW1>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/3
-------------------------------
-----------------------------
IPsec policy: map1
Sequence number: 10
Alias: template-temp1-10
Mode: Template
-----------------------------
Tunnel id: 1
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Transmitting entity: Responder
Path MTU: 1436
Tunnel:
local address/port: 10.1.1.1/4500
remote address/port: 102.1.1.2/1025
Flow:
sour addr: 192.168.10.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.20.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 2205382650 (0x837377fa)
Connection ID: 81604378625
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842414/1585
Max received sequence-number: 9136
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: Y
Status: Active
[Outbound ESP SAs]
SPI: 17477209 (0x010aae59)
Connection ID: 81604378624
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842414/1585
Max sent sequence-number: 9136
UDP encapsulation used for NAT traversal: Y
Status: Active
-------------------------------
Interface: GigabitEthernet1/0/3
-------------------------------
-----------------------------
IPsec policy: map1
Sequence number: 10
Alias: template-temp1-20
Mode: Template
-----------------------------
Tunnel id: 2
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Transmitting entity: Responder
Path MTU: 1436
Tunnel:
local address/port: 10.1.1.1/4500
remote address/port: 103.1.1.1/4500
Flow:
sour addr: 192.168.10.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.30.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 558262863 (0x21466a4f)
Connection ID: 90194313219
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842377/1531
Max received sequence-number: 9572
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: Y
Status: Active
[Outbound ESP SAs]
SPI: 1974871094 (0x75b62436)
Connection ID: 90194313218
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842377/1531
Max sent sequence-number: 9572
UDP encapsulation used for NAT traversal: Y
Status: Active
<FW1>
在FW1上观察到,NAT-T都是 Y
FW2上查看信息
<FW2>dis ike sa
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
ID Profile Remote Flag Remote-Type Remote-ID
--------------------------------------------------------------------------------
11 profile1 101.1.1.1 RD FQDN zongbu
<FW2>
<FW2>dis ike sa ver
-----------------------------------------------
Connection ID: 11
Outside VPN:
Inside VPN:
Profile: profile1
Transmitting entity: Initiator
Initiator cookie: 4a8ad70544712029
Responder cookie: cee73f6122f5b8b8
Output interface name:
-----------------------------------------------
Local IP/port: 192.168.20.200/4500
Local ID type: FQDN
Local ID: fenzhi-1
Remote IP/port: 101.1.1.1/4500
Remote ID type: FQDN
Remote ID: zongbu
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: 3DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 84794
Exchange-mode: Main
Diffie-Hellman group: Group 1
NAT traversal: Detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index:0xffffffff
Vendor ID sequence number:0x0
<FW2>
<FW2>dis ipsec sa bri
-----------------------------------------------------------------------------
Tunnel-ID Name Dst Address(port) Protocol SPI
-----------------------------------------------------------------------------
0 map1-10 <101.1.1.1(4500) ESP 17477209
0 map1-10 >101.1.1.1(4500) ESP 2205382650
<FW2>
<FW2>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/3
-------------------------------
-----------------------------
IPsec policy: map1
Sequence number: 10
Alias: map1-10
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Transmitting entity: Initiator
Path MTU: 1436
Tunnel:
local address/port: 192.168.20.200/4500
remote address/port: 101.1.1.1/4500
Flow:
sour addr: 192.168.20.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.10.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 17477209 (0x010aae59)
Connection ID: 98784247809
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842396/1455
Max received sequence-number: 9345
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: Y
Status: Active
[Outbound ESP SAs]
SPI: 2205382650 (0x837377fa)
Connection ID: 98784247808
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842396/1455
Max sent sequence-number: 9345
UDP encapsulation used for NAT traversal: Y
Status: Active
<FW2>
FW3上查看信息
<FW3>dis ike sa
Flags:
RD--READY RL--REPLACED FD-FADING RK-REKEY
ID Profile Remote Flag Remote-Type Remote-ID
--------------------------------------------------------------------------------
8 profile1 101.1.1.1 RD FQDN zongbu
<FW3>dis ike sa ver
<FW3>dis ike sa verbose
-----------------------------------------------
Connection ID: 8
Outside VPN:
Inside VPN:
Profile: profile1
Transmitting entity: Initiator
Initiator cookie: b3ef914a89aa888a
Responder cookie: 168da67159b7262f
Output interface name:
-----------------------------------------------
Local IP/port: 103.1.1.1/4500
Local ID type: FQDN
Local ID: fenzhi-2
Remote IP/port: 101.1.1.1/4500
Remote ID type: FQDN
Remote ID: zongbu
Authentication-method: PRE-SHARED-KEY
Authentication-algorithm: SHA1
Encryption-algorithm: 3DES-CBC
Life duration(sec): 86400
Remaining key duration(sec): 84212
Exchange-mode: Aggressive
Diffie-Hellman group: Group 1
NAT traversal: Detected
Extend authentication: Disabled
Assigned IP address:
Vendor ID index:0xffffffff
Vendor ID sequence number:0x0
<FW3>
<FW3>dis ipsec sa bri
-----------------------------------------------------------------------------
Tunnel-ID Name Dst Address(port) Protocol SPI
-----------------------------------------------------------------------------
0 map1-10 <101.1.1.1(4500) ESP 1974871094
0 map1-10 >101.1.1.1(4500) ESP 558262863
<FW3>
<FW3>dis ipsec sa
-------------------------------
Interface: GigabitEthernet1/0/2
-------------------------------
-----------------------------
IPsec policy: map1
Sequence number: 10
Alias: map1-10
Mode: ISAKMP
-----------------------------
Tunnel id: 0
Encapsulation mode: tunnel
Perfect Forward Secrecy:
Inside VPN:
Extended Sequence Numbers enable: N
Traffic Flow Confidentiality enable: N
Transmitting entity: Initiator
Path MTU: 1436
Tunnel:
local address/port: 103.1.1.1/4500
remote address/port: 101.1.1.1/4500
Flow:
sour addr: 192.168.30.0/255.255.255.0 port: 0 protocol: ip
dest addr: 192.168.10.0/255.255.255.0 port: 0 protocol: ip
[Inbound ESP SAs]
SPI: 1974871094 (0x75b62436)
Connection ID: 30064771073
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842352/1474
Max received sequence-number: 9867
Anti-replay check enable: Y
Anti-replay window size: 64
UDP encapsulation used for NAT traversal: Y
Status: Active
[Outbound ESP SAs]
SPI: 558262863 (0x21466a4f)
Connection ID: 55834574848
Transform set: ESP-ENCRYPT-DES-CBC ESP-AUTH-SHA1
SA duration (kilobytes/sec): 1843200/3600
SA remaining duration (kilobytes/sec): 1842352/1474
Max sent sequence-number: 9867
UDP encapsulation used for NAT traversal: Y
Status: Active
<FW3>